iPhone has introduced the new iOS 17.3 update with enhanced security features, especially intended to shield users from thefts.
Apple Stolen Device Protection requires biometric authentication while a user is not in their home or place of employment.
Let’s see how to use this latest feature!

How to Turn on Apple Stolen Device Protection Setting on iPhone/iPad
iPhone Stolen Device Protection was introduced following WSJ’s Joanna Stern’s investigation that shows an increase in iPhone thefts in public spaces like parks or bars.
Attackers would usually observe victims inputting their passcodes before taking possession of their iPhones. They would then use this information to immediately change the owners’ Apple ID passwords, locking them out of their respective accounts along with iCloud backups.
Therefore, it’s become more important than ever to turn it on so you never have to worry about your privacy. Follow the steps to turn on Apple Stolen Device Protection:
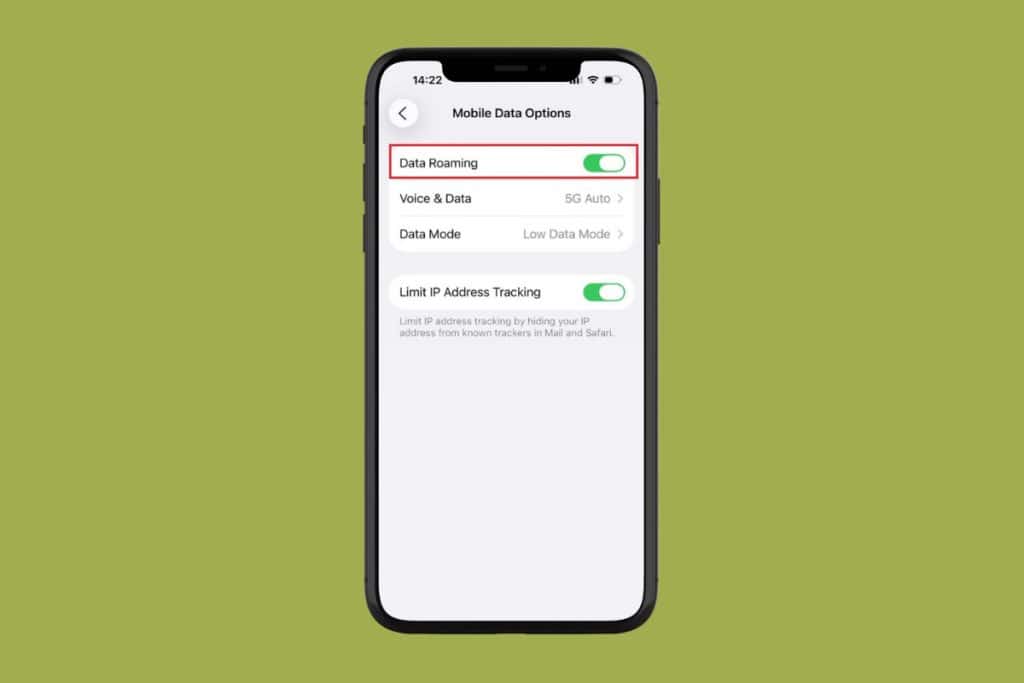
1. Go to Settings and tap on Face ID & Passcode.
2. Enter your device passcode.
3. Tap on Stolen Device Protection to turn it on.

Also Read: How to Reset Apple ID Security Questions
Apple Stolen Device Protection Mode Features & Benefits
Smartphones have become so essential to our daily lives that losing one can be catastrophic as well as costly.
There’s an added stress of how your information can be misused in cases of theft.
Therefore, the new security feature on Apple devices will make sure only the owner of the device is using the phone when they are not in familiar locations. Let’s check out its features:
- Biometric Authentication Using Face ID or Touch ID: Certain operations, such as retrieving credit cards, and stored passwords, will need a single biometric authentication using Touch ID or Face ID. Remember, there is no backup or alternate passcode you can only utilize these two features.
- Security Delay: You must wait an hour before completing another round of Face ID or Touch ID authentication while updating your Apple ID password.
You might be thinking why is this extra layer of security so important? Here are some benefits that might make you turn on this feature:
- It helps thieves from not making critical changes to the phone in case they are aware of your passcode.
- It ensures only the owner of the device can change sensitive information like stored passwords, wallet codes, or saved credit card information.
- Additionally, it prevents thieves from exploiting stored payment methods to make purchases.
How does Stolen Device Protection Truly Work?
When your iPhone is not in accustomed surroundings, like residence or work, certain operations require extra security when Stolen Device Protection is activated.
If you’re wondering exactly what actions will require authentications before you turn on this feature, we’re here to clear your doubt. You have to authenticate with Face or Touch ID in cases of:
- Use passwords or passkeys saved in Keychain
- Erase all content and settings
- Use payment methods saved in Safari
- Apply for a new Apple Card
- Turn off Lost Mode
- Take certain Apple Cash and Savings actions in the Wallet
- View Apple Card virtual card number
- Use your iPhone to set up a new device
As stated below, security delay will be activated under these circumstances:
- Change your Apple ID password
- Sign out of your Apple ID
- Update Apple ID account security settings
- Change your iPhone passcode
- Add or remove Face ID or Touch ID
- Turn off Find My
- Reset all settings
- Turn off Stolen Device Protection
Also Read: How to Fix Apple Watch Stuck on Please Continue Setup on iPhone
With the Stolen Device Protection feature, Apple has yet again shown that it does not compromise when it comes to security.
This marks another step in the fight to tackle phone theft and ensure users don’t have the added stress of how their sensitive information can be used against them.
Reach out to us in the comment section if you have any queries or suggestions. Keep visiting TechCult for the latest tech walkarounds.