Experiencing frequent web browser redirects to unfamiliar or suspicious sites? Are these redirects leading to e-commerce or gambling sites, accompanied by numerous ad pop-ups? This could indicate the presence of the Google Redirect Virus, known for its persistent and unwanted redirects and pop-ups. The malware may not be considered deadly, yet quite annoying. This step-by-step guide explains how to handpick and manually remove the Google redirect virus.

Why is it tough to remove? How to Remove Google Redirect Virus Manually
It is actually a rootkit and not a virus. The rootkit cleverly embeds itself within crucial Windows services which makes it work like an operating system file. This makes it difficult to identify the infected file or code. Moreover, the malware is coded in such a way that it creates different variants from the same code from time to time. This makes it difficult for the security software to catch the code and release a security patch. Even if they succeed in creating a patch, it becomes ineffective if the malware attack again which contains a different variant.
The Google redirect virus extends beyond Google, affecting Yahoo and Bing searches too along with with recent variants, like “Nginx Redirect Virus” and “Happili Redirect Virus”. As of May 2016, the Google redirect virus had already infected more than 60 million computers wide, out of which 1/3rd is from the US.
Note: Please try these steps at your own risk however, steps mentioned above won’t crash your computer. But to be on the safe side, it is better to take a backup of important files or system restore and ensure that you have the option to repair or re-install the operating system using OS disk.
Option I: Try online tools or go to professionals
There are plenty of security tools available in the market. While some users had success in removing the infection using one software, the same may not work on another computer or virus. It is highly recommended to take a backup of important data before trying any tools to be on the safe side. You can also get help from professionals who specialize in removing this infection – authorised service center and not geek squad.
Option II: Try to remove the virus manually
There is no easier way to remove an infection other than running a scan using software and fixing it. But if it fails, the last resort is to try removing the infection manually. Manual removal method is time-consuming and hard to follow because of its technical nature. Some users might find the troubleshooting mentioned here complicated. Let’s face it, the infection itself is complicated and even the experts struggle in order to get rid of this infection.
Step 1. Enable Hidden Files through Folder Options
Operating system files are hidden by default to prevent accidental deletion. Infected files try to hide among the OS files. So it is advised to unhide all hidden files before starting troubleshooting:
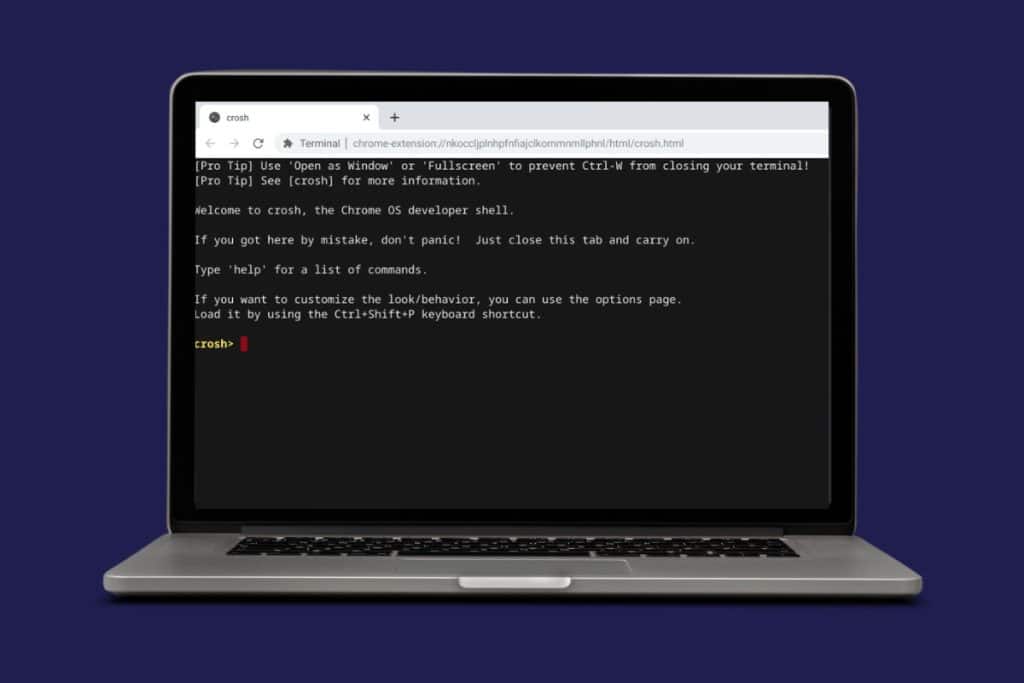
1. Press Windows Key + R for opening Run dialog box.

2. Type Control folders
3. Click View tab.
4. Enable show hidden files, folders and drives

5. Uncheck hide extensions for known file types
6. Uncheck hide protected operating system files
Step 2. Open Msconfig to Enable Bootlog file
This bootlog file will be needed in the last step.
1. Open Run window, type msconfig and click Ok.

3. Click Boot tab if you are using Windows 10, 8 or 7. In you are using Win XP, select boot.ini tab
4. check bootlog to enable it
5. Click Apply and click OK
Also Read: Top 11 Ways to Fix Virus Scan Failed Error in Google Chrome
Step 3. Restart Computer
Restart the computer for making sure that the changes you made are implemented. On restarting the computer a file ntbttxt.log is created which is discussed later on.

Step 4. Do Complete IE optimization
Internet explorer optimization is done to ensure that redirection is not caused by a problem in the web browser or corrupted internet settings that connects the browser online. If optimization is done properly, the browser and internet settings are reset back to original defaults.
Note: Some of the internet settings found while doing IE optimization are common for all browsers. So, it doesn’t matter if you use Chrome, Firefox, Opera, etc., it is still recommended to do an IE optimization.
Optimizing Internet Explorer involves several steps to enhance its performance which are listed below:
- Update IE: Ensure you have the latest version to access new features and security patches.
- Clear Cache and Cookies: Go to Internet Options > General tab > Browsing History > Delete to Clear cache, cookies, and temporary files.
- Manage Add-ons: Disable unnecessary toolbars and add-ons via Manage Add-ons in the Tools menu.
- Reset IE settings: In Internet Options, go to the Advanced tab and click Reset to revert IE settings to default.
- Security Settings: Adjust security settings to a balanced level for safety without hindering browsing.
- Disable Unnecessary Services: Disable automatic checking for feeds, web slices, and add-ons not in use.
- Optimize Performance: Limit the number of tabs open simultaneously to enhance browsing speed.
- Update Plugins: Ensure plugins like Flash, Java, and others are up-to-date for security and performance.
- Check for Malware: Run a thorough antivirus and anti-malware scan regularly to detect and remove any threats.
Step 5. Check Device Manager
Device Manager is a Windows tool that lists all the devices inside your computer. Some infections are capable of hiding hidden devices which can be used for malware attack. Check it to find any infected entries as follows:
1. Open Run window (Windows Key + R)
2. Type devmgmt.msc
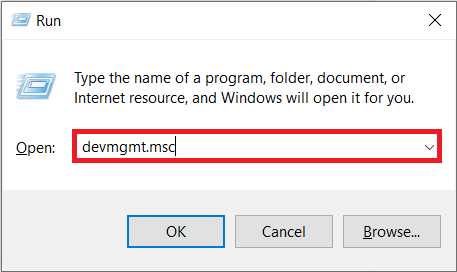
3. Click View tab on the top
4. Select show hidden devices
5. Look for non-plug and play drivers. Expand it to see the entire list under option.
6. Check for an entry named TDSSserv.sys. If you don’t have the entry, look for any other entries which look suspicious.
Note: If you can’t make up your mind about an entry is good or bad, then do a Google search with the name to find if it is genuine.
7. If the entry is found to be an infected one, right-click on it and then click uninstall.
Note: Once the uninstall is complete, don’t restart the computer yet. Continue troubleshooting without restarting.
Also Read: How to Remove a Virus from a Windows 11 Computer
Step 6. Check Registry
Check for the infected file inside the registry:
1. Open Run window and type regedit to open registry editor

2. Click Edit > Find
3. Enter the infection name. If it is a long one, enter the first few letters of infected entry
Example: Click on edit –> find. Enter the first few letters of the infection name. In this case, I used TDSS and searched for any entries starting with those letters. Every time there is an entry starting with TDSS, it shows the entry on the left and the value on the right side.
4. If there is just an entry, but no file location mentioned, then delete it directly. Continue searching for next entry with TDSS
The next search took me to an entry that got details of file location on the right which says C:\Windows\System32\TDSSmain.dll.You need to utilize this information. Open folder C:\Windows\System32, find and delete TDSSmain.dll mentioned here.
5. Assume that you were not able to find the file TDSSmain.dll inside C:\Windows\System32. This shows entry is super hidden. You need to remove the file using the command prompt. Just use the command to remove it: del C:\Windows\System32\TDSSmain.dll
6. Repeat the same until all entries in the registry starting with TDSS is removed. Make sure if those entries are pointing towards any file inside the folder remove it either directly or by using the command prompt.
If you were not able to find TDSSserv.sys inside hidden devices under device manager, then go to Step 7.
Step 7. Check ntbtlog.txt log for corrupted file
In step 2, a log file called ntbtlog.txt was generated inside C:\Windows. It’s a small text file containing a lot of entries which might run to more than 100 pages if you take a printout. You need to scroll down slowly and check if you have any entry for TDSSserv.sys which shows that there is an infection. Follow the steps mentioned in Step 6 to remove the same.
In the above-mentioned case, I mentioned only about TDSSserv.sys, but there are other types of rootkits that do the same damage. Let’s take care of 2 entries H8SRTnfvywoxwtx.sys and _VOIDaabmetnqbf.sys listed under device manager in my friend’s PC. The logic behind understanding if it is a dangerous file or not is mainly by their name. This name makes no sense and I don’t think any self-respecting company will give a name like this to their files. Here, I used the first few letters H8SRT and _VOID and did the steps mentioned in Step 6 to remove the infected file.
(Please Note: H8SRTnfvywoxwtx.sys and _VOIDaabmetnqbf.sys are just an example. The corrupted files can come in any name, but it will be easy to recognize because of the long file name and the presence of random numbers and alphabets in the name.)
Recommended: How to Remove a Virus from an Android Phone
You now have clear instructions including step by step guide on how to get rid of the Google redirect virus. Also, you know what to do if this didn’t work out. Take action immediately before the infection spreads to more files and renders the PC unusable. Share this tutorial as it makes a huge difference to someone facing the same problem.